In our Manufacturing Simplified series, we reach out to the brightest minds in the industry to explain the world of manufacturing in terms we mere mortals can understand. This post’s focus: Operational Technology.
When I first reached out to Dave Griffth to write this article, I’ll be honest: I was a bit uncertain about how technology worked in the manufacturing world.
I understand technology from a marketing perspective: SEO, social media, and websites are all part of the digital marketing approach we take with our clients. But understanding how IT integrates into the operational world for manufacturers was a different story.
Computers have controlled machinery for decades, but the Internet and wireless systems are opening up new realms of possibilities for manufacturing. They’re part of the digital transformation taking place in manufacturing, and to be a part of the industry, I wanted a deeper understanding of how it works.
Dave Griffith seemed like a natural go-to for an answer. Dave is the owner of Capelin Solutions, and he helps deliver software solutions, typically in the industrial or manufacturing environment. He’s also the co-host of Manufacturing Hub with Dave & Vlad, a podcast about “all things Industrial Automation.”

Dave Griffith
My goal in collaborating with this article: We’re going to attempt to explain the technology landscape to an executive at a company, someone who, as Dave puts it, “wants to know the basics, but really doesn’t care how it works.”
The big picture starts with a big diagram: The Purdue Model
When I learned about geography, my teachers used a map. For this lesson in technology, we’ll use a diagram: The Purdue Model.
Its origin traces back to the 1990s, when Theodore J. Williams and members of the Industry-Purdue University Consortium for Computer Integrated Manufacturing Purdue Enterprise Reference Architecture (PERA) decided to create a reference model for IT enterprise architecture.
Their goal: “PERA provides a way to break down enterprises into understandable components, to allow staff at all levels to see the ‘20,000 ft view’ as well as to describe the details that they see around them every day.” (Source: PERA Enterprise Integration Website)
They created what’s referred to as the Purdue Model. It’s shown here in this graphic created for Automation World:
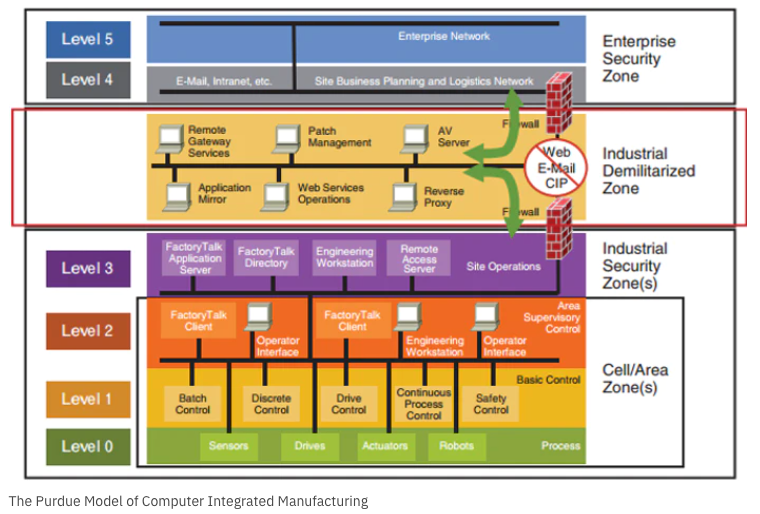
Sorry, this graphic looks like someone was over served on IT jargon and threw this thing up. So let’s simplify the Purdue Model graphic and the descriptions that follow. Take a look at a far less techie overview:
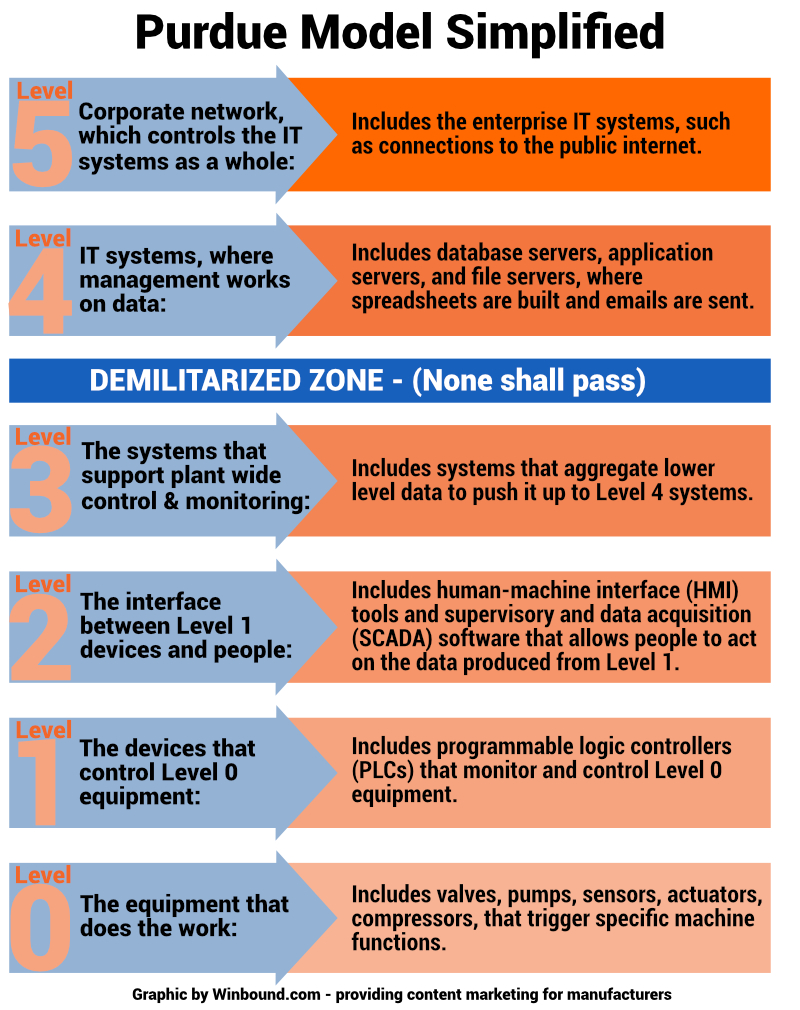
- Level 0 — The equipment that does the work
Includes valves, pumps, sensors, actuators, and compressors that trigger specific machine functions.
- Level 1 — The devices that control Level 0 equipment
Includes programmable logic controllers (PLCs) that monitor and control Level 0 equipment.
- Level 2 — The interface between Level 1 devices and people
Includes human-machine interface (HMI) tools and supervisory and data acquisition (SCADA) software that allows people to act on the data produced from Level 1.
- Level 3 — The systems that support plant-wide control and monitoring
Includes systems that aggregate lower level data to push it up to Level 4 systems.
DEMILITARIZED ZONE – (None shall pass)
- Level 4 — IT systems, where management works on data
Includes database servers, application servers, and file servers, where spreadsheets are built and emails are sent.
- Level 5 — Corporate network, which controls the IT system as a whole
Includes the enterprise IT systems, such as connections to the public Internet.
Why the different levels? As Griffith explains, “This was a theoretical model to show how the plant floor, and how it was going to be physically air-gapped from the Internet/outside world.”
The “air-gapping” was built in as a level of security with a burgeoning Internet back in the 90s. You’ll notice the “Industrial Demilitarized Zone” that appears between Levels 3 and 4. This zone was meant to provide separation between the plant floor IT levels and the Internet.
How Operational Technology pushes data up the levels
Now that you see the big picture in terms of the IT architecture, let’s dive into how these different areas are working and evolving. That requires introducing a technology term that’s often used in the manufacturing world: Operational Technology.
Gartner defines Operational Technology (OT) as “hardware and software that detects or causes a change, through the direct monitoring and/or control of industrial equipment, assets, processes and events.” OT hardware and software is employed throughout the Purdue Model.
On Level 1, for example, OT professionals first used edge computing (a form of computing done on site or near a particular data source), to tap into the PLCs (programmable logic controllers) on a machine level.
Operations and management then wanted to access the data being generated in Levels 0 and 1, which led to supervisory control and data acquisition (SCADA) software in Level 2.
OT seemed to follow a natural progression of pushing data up levels, from the controllers initiating action to the software systems that could monitor data and allow for user interface. It included that buffered demilitarized zone, which kept floor data separate from the Internet for security reasons.
This cybersecurity measure made sense, but then along came the Industrial Internet of Things (IIoT).
The cloud and IIoT: The kindly Death Star
This orderly transfer of data became disrupted with the advent of cloud computing and the Industrial Internet of Things (IIoT).
Because you could enable devices to become wireless and accessible by the Internet, the idea of edge computing, where you put powerful computing devices next to the Level 0 equipment, became irrelevant.
Now you could deploy your vast computing power to the cloud, and access any device, anywhere.
Think of it as a kindly Death Star. Instead of shooting out a deadly laser beam to blow up a planet, the kindly Death Star uses a more benevolent tractor beam to extract data. That data can be used by the powerful computers on the kindly Death Star to analyze processes and improve performance on the planet below.
Trudging information up through the levels is no longer needed. You can reach management at Level 4 instantly and cost-effectively.
Now we can pull from the very bottom, push it to the cloud, then push it back down. We can run huge amounts of calculations at much smaller costs.
Is the Purdue Model now obsolete?
With this new paradigm, IT theorists have attempted to reimagine the Purdue Model and its traditional hierarchies. But Griffith doesn’t see the model being dismissed entirely, largely because of two glaring issues: Cybersecurity and costs.
Cybersecurity: The demilitarized zone in the Purdue Model was created for a reason. The chaos of opening access to device operating systems can render an organization vulnerable to hackers.
When you’re talking about Operational Technology, you’re talking about the operation of actual machinery. Do manufacturers really need another level of complexity for keeping operators safe on the plant floor?
Overall, the task of securing existing access points to the Internet has been a big enough headache. Why would you add countless more to the equation?
Cost: You could add in additional cybersecurity measures as part of the escalating costs of IIoT, but Griffith also brought up an aspect most manufacturers might not be considering: The functionality of current machinery.
“We still have a lot of people running a 50-year old PLC on the plant floor,” he points out.
Some of the PLCs are not able to be networked. Some are not cost-effective to do so. It might be a better decision to replace them as part of a larger initiative.
That’s why Griffith doesn’t see some of the pie-in-the-sky revisions of the Purdue Model to be accurate.
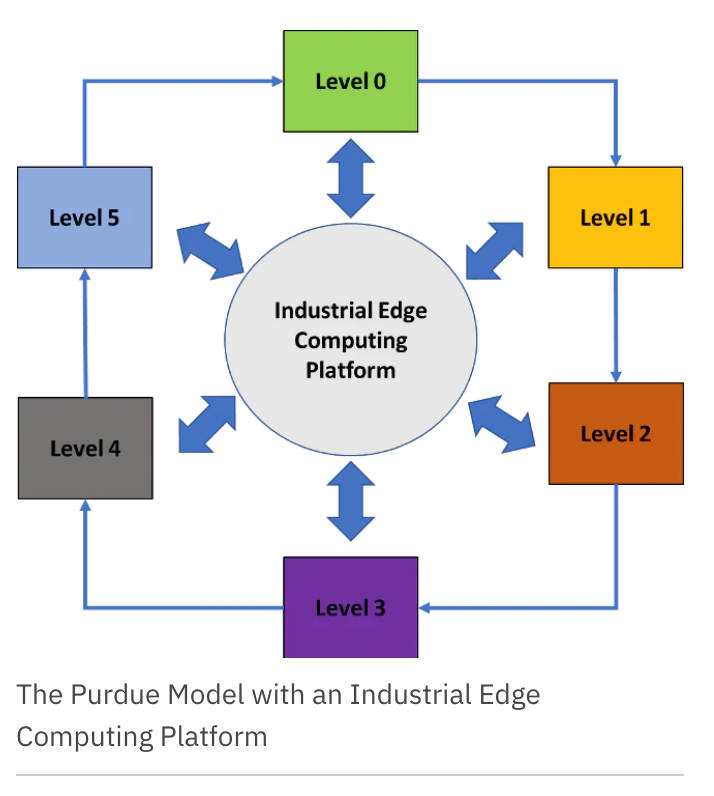
For example, Vatsal Shah, CEO of Litmus, proposed a model like the one below in Automation World, in which an industrial edge computing software can be used to gather data in the cloud, where a platform can ensure control and security.
Griffith doesn’t disagree with the theory behind this type of approach, but rather its pragmatism. The problem is those individual pieces of equipment, and the eventual need for creating specific software patches for evolving security threats.
Those patches would all need to be updated, on a continual basis. Griffith imagines this would take an immense amount of time and resources. The net result: Before you could even get to analyzing the data, you’d have spent all your resources trying to protect it in the first place.
The path forward: Take edible bites
When assessing the current IT and OT landscape of manufacturing, Griffith feels like we may be skipping a decade in our rush to access data. “I tell most people that we don’t have to be bleeding edge,” he says.
Most manufacturers are stuck in 1997. We can follow the playbook for 2010.
Griffith is referring to taking 2020 technology and putting an industrial spin on it. For example, you can use a $300 iPad for diagnosing a service issue on a machine. Just taking a walk on the plant floor and identifying problems is a good place to start with a technology problem.
“Many manufacturers are still using pen and paper to record data from their machines,” Griffith notes. Creating software specifically for that machine’s PLC and transferring it to the cloud can be a step in the right direction. And if you limit it to your critical machines, then you don’t necessitate multiple security patches.
Software as service providers are taking this approach. They’re also looking at other ways to move companies from 1997 to 2010. Copia Automation, for example, has developed a way for manufacturers to back up the GIT programming language that controls their machines.
“GIT has been around since 2005,” Griffith said. “Copia has done a nice job of just ensuring that you can back up that programming language whenever you make changes.” These types of IT fundamentals — aka DevOps — might be common in other industries, but not in manufacturing.
Griffith believes these are “edible bites,” and we can expect many more of them to occur moving forward.
The big picture in IT and OT for manufacturing isn’t about disruption, like we’ve seen in far more technologically advanced verticals. Our focus should be about modernization, and as Griffith notes, even making it to 2010 will be a giant step in the right direction.